Products
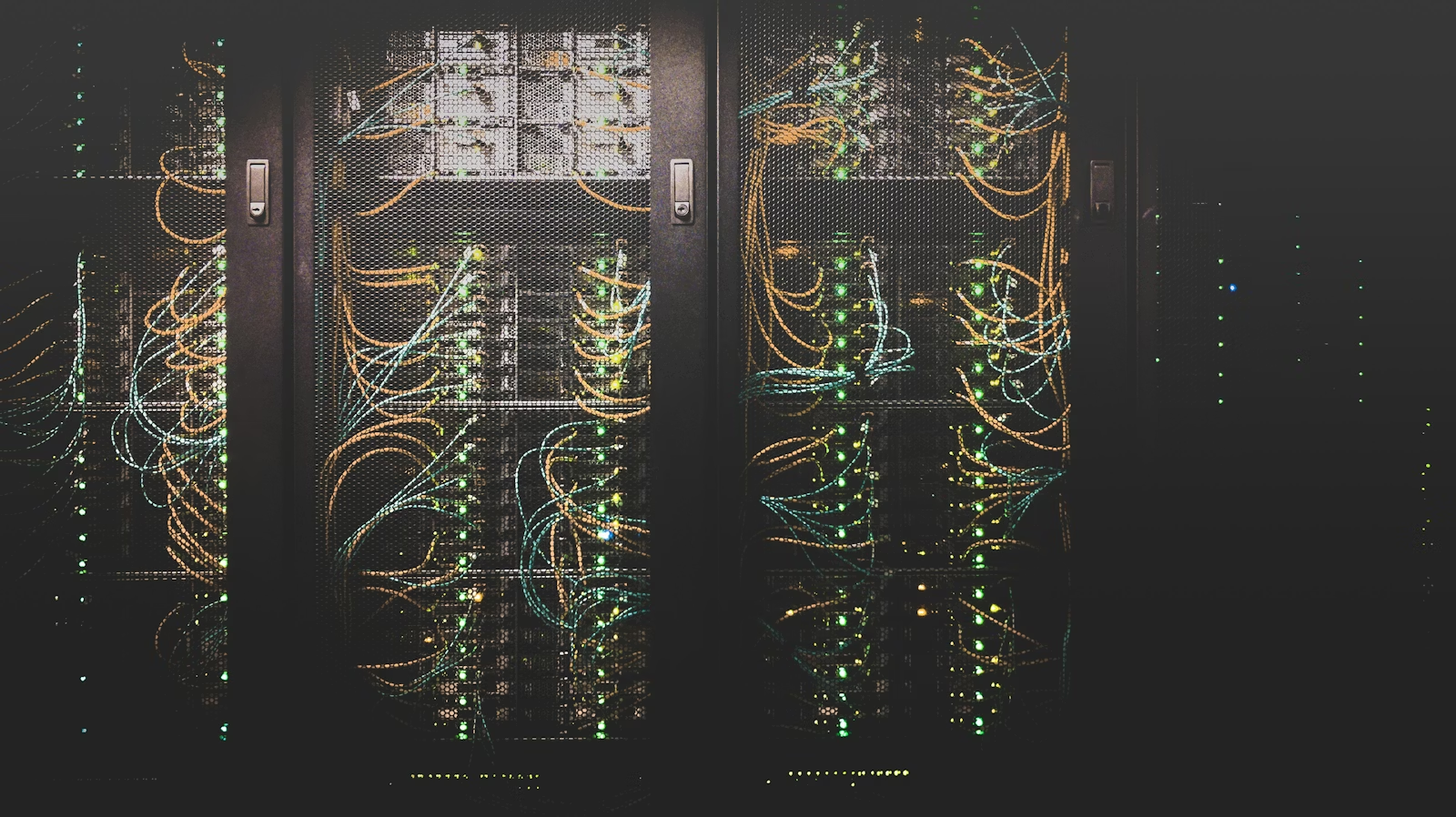
Design and run cloud estates—private, public, hybrid, and edge—with security and observability baked in. Landing zones, migrations, performance footprints, and resilient backup tiers sized honestly.
Talk to our team ⟶Cloud — explore solutions
Design and run cloud estates—private, public, hybrid, and edge—with security and observability baked in. Landing zones, migrations, performance footprints, and resilient backup tiers sized honestly.
PaaS
Cloud-native controls and posture management aligned to how your teams actually build and ship workloads.
Infrastructure
Compute and storage footprints tuned for demanding databases, analytics, and throughput-heavy workloads.
PaaS
Dedicated capacity and isolation patterns for regulated apps, predictable performance, and tenant boundaries.
Infrastructure
Backup immutability, replication tiers, and HA designs that translate into real RPO/RTO commitments.
PaaS
Processing closer to users and machines—lower latency, offline resilience, and sane data gravity.
PaaS
Consistent networking, identity, backup, and observability across on-prem footprints and public clouds.
PaaS
Landing zones, migrations, and operational guardrails on hyperscalers without slowing builders down.
Cloud posture
Landing zones, identity, resilience, and cost discipline—expressed as operational work your teams can run, not slide assertions.
Subscriptions, guardrails, and network egress patterns scoped to blast radius—with accountable owners per environment.
Directory synchronization, conditional access, and break-glass posture tested against how apps actually authenticate.
Backup tiers, immutability, and failover drills mapped to RPO/RTO claims—not job-complete ticks alone.
Showback, tagging discipline, and rightsizing cadence procurement can recognize—without drowning operators in dashboards.
Latency, residency, and disconnected scenarios handled honestly before architecture diagrams freeze commitments.
Change records, access reviews, and incident timelines structured so audits and boards get narrative—not raw exports.
Hybrid identity, landing zones, edge, and backup posture—how cloud services connect before you open a specific tile.
Teams comparing private, public, and hybrid cloud usually need orientation before selecting a specific service. This page covers context, delivery model, timing, and fit before listing each cloud offering.
Use this page when someone needs to forward a single URL that explains the whole portfolio before deep-diving individual architectures.
Landing zones age while developers route around them. Backups exist but restores fail in drills. Hybrid connectivity becomes a maze of NAT exceptions. Finance discovers egress bills nobody modeled.
These failures look technical but are organizational: unclear ownership between platform, security, and application teams; incentives that reward shipping features over operational rigor.
Platforms and patterns we operate across private, public, hybrid, and edge footprints.We design, migrate, secure, and operate cloud and hybrid estates spanning private platforms, hyperscalers, colocation, and edge sites constrained by latency, residency, or uptime.
Our work ties architecture to operational truth—patch cadence, incident response, cost guardrails, recovery rehearsals—not diagrams that ignore who holds the pager.
Controls tied to CI/CD, IaC, and workload ownership—not shelf PDFs
Networking, identity, logging, and cost visibility operators can defend
Local footprint when offline resilience or millisecond latency rules out pure central cloud
Databases and analytics estates sized with honest capacity and failover discipline
Architectures validated through executed restore drills—not green backup jobs alone
Chargeback or showback narratives finance and platform leads can explain in one page
Discovery anchored to blast radius, migrations with rollback, run-state tied to named services.
Discovery inventories workloads, data classes, regulatory triggers, and existing operational maturity. We refuse to sequence migrations that skip dependency mapping.
Build phases land thin slices—network identity baseline, golden paths for standard workloads, automated guardrails—each reviewed by security and finance before expansion.
Run phases include operational handoffs: monitoring dashboards executives can read, change windows that respect business calendars, and quarterly hygiene reviews on keys, certificates, and unused capacity.
Shared-responsibility clarity across landing zones, workloads, and SaaS means controls attach to actual build pipelines—not PDF diagrams nobody operates.
Exceptions with owners, and evidence exports suitable for GRC cadence
Not generic CIS PDFs
And encryption posture traced to named workloads and regions
Cloud economics and uptime stories crack when restores fail, egress surprises finance, or blast radius grows unchecked—we tie architecture to rehearsed failure modes.
Not green backup jobs alone
Tagging discipline, and capacity signals finance can defend
And rollback paths sized for maintenance windows you actually take
Migration mandates, blast-radius surprises, residency questions, or latency-bound workloads.
Use case
Without an accountable migration factory
Use case
Exposed backup theater
Use case
And overlapping VPCs
Use case
Without tagged ownership
Use case
And nobody could produce it quickly
Use case
Pure public-cloud round trips
We optimize for defendable decisions—architecture reviewers can trace every assumption to an owner and a test.
Engineers stay through operational transition; we do not disappear after Terraform applies.
Review tiles above, browse the full catalog, or talk to us about scope.
Talk to our team about scopeBrowse the full product catalogNot checkbox PDFs
Degraded modes, rollback paths, blast-radius containment
Without turning cloud into a frozen bureaucracy
Tell us workloads and constraints—we map landing zones, migrations, and resilience without vendor theater.
We work across hyperscalers, colocation, edge stacks, and your existing observability—landing zones and migrations respect tooling finance already licenses.
Jump to this category’s tiles, the full catalog, or contact.
Talk to our team about scopeBrowse the full product catalogWhen hybrid connectivity is load-bearing
Or showback politics you navigate
After day-two drift